Tagged: header
-
AuthorPosts
-
November 1, 2019 at 6:53 pm #1153114
i started to secure my different sites by adding different header entries via htaccess file.
when inserting Content-Security-Policy header some options in Enfold Options didn’t work as expected.# Extra Security Headers <IfModule mod_headers.c> Header set Content-Security-Policy "default-src 'self';" </IfModule>i have to find a whitelist now for google maps and some other things – but i thought that all inline css and scripts are loaded over https per default.
you can check your site f.e. here: https://securityheaders.com/
one trouble seems to come from using in plugins the
plugin_dir_url( __FILE__ )for the assets path – sometimes this ends in http loading and mixed content message – and unsecure messages from the browser window.
how to solve this above and f.e. the plugins problematicEdit: i know that this maybe more or less a wordpress topic – but i do not know a lot of developers and coders like f.e. Günter ;)
maybe he have a hint for me.November 1, 2019 at 8:04 pm #1153121My efforts for now: i did setup for the admin area an own htaccess file with less restrictions.
That is good for the options in enfold – but there is a lot to do to have a secure site – and white lists for google maps f.e. etc.
If someone has a good example page – it would be nice to see.November 1, 2019 at 9:53 pm #1153138Ok _ thanks for now :
these are my efforts on that: https://securityheaders.com/?q=https%3A%2F%2Fwebers-webdesign.de%2F
you can see my code inserted in htaccess file on that page.November 5, 2019 at 12:15 pm #1153969so these settings works very well – but had to be always adjusted to your website.
The best would be to start with a Standard Entry in htaccess file# Extra Security Headers <IfModule mod_headers.c> Header set X-XSS-Protection "1; mode=block" Header always append X-Frame-Options SAMEORIGIN Header set X-Content-Type-Options nosniff Header set Strict-Transport-Security "max-age=31536000; includeSubDomains; preload" Header set Referrer-Policy no-referrer Header set Feature-Policy "camera 'none'; microphone 'none'; payment 'none';" Header set Content-Security-Policy "default-src 'self'; img-src 'self' http: https: *.gravatar.com;" </IfModule>Do not insert this between the standard Entry of WordPress itself:
Between # BEGIN WordPress and # END WordPressAfter that you look to your site and open the developer tools of your browser – goto console log and look for errors.
If you have a youtube film – f.e. you have to exclude these sources from the Content-Security-Policy
you see that on the code above f.e. the gravatar.com is excluded from img-src .
Google Maps needs to have contact to api etc. pp.November 7, 2019 at 11:26 am #1154577Why is it necessary to set the script-src to ‘unsafe-inline’ and ‘unsafe-eval’ – in content security policy ?
without it does not work – same thing with style-src .
My whole website is https – i force it via wp-config and on htaccess there are entries too!
But when i set the given CSP to only ‘self’ a lot of things do not work.November 11, 2019 at 9:38 pm #1155764Hi,
Gunter will check this, but it seems that this is not only based on us, but also how for example redux is working.
This would need a little bit of digging to find out all the things required to fix, but we appreciate all the input.Best regards,
BasilisNovember 12, 2019 at 10:26 am #1155949Most people do forget to set these helpfull headers. Many of the known attack possibilities ( man in the middle , cross-site-scripting etc.) are almost impossible then.
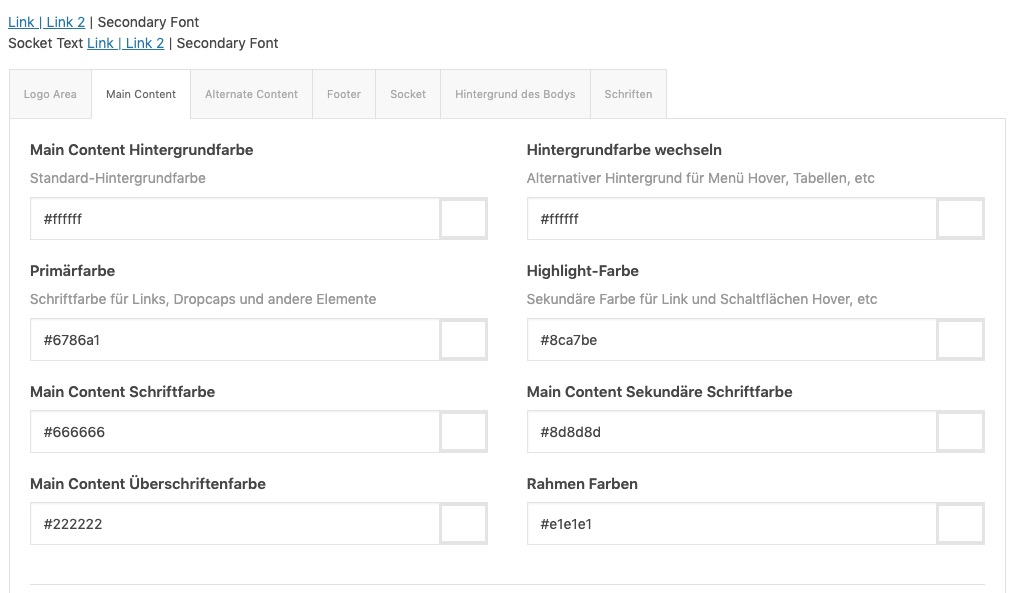
It just needs some reworking, since everyone wants to have different features on his site; (Google Maps, Google Analytics, Youtube, Vimeo, CDNs to present media files).What I’m only surprised about is that some things I thought were covered by the ‘self’ setting, which is not the case (script loading and stylesheet loading). To have normal outlook of Enfold options i had to set for:
script-src ‘self’ ‘unsafe-eval’ ‘unsafe-inline’
style-src ‘self’ ‘unsafe-inline’So I allow scripts and stylesheets to be loaded insecurely inline (http).
My guess was that some of these get parameters ( https://codex.wordpress.org/Determining_Plugin_and_Content_Directories ) are causing insecure loading. Because i force my whole site to be https by wp-config entry – i have these inconsistancies – like the image above shows you.
November 22, 2019 at 7:20 pm #1159304Hi,
I too have run into issues with with security headers and the use of ‘self.’ I’m guessing it is WordPress related and not theme as I also run sites built on Avada and the same happens. Using the ‘self’ in CSP for some reason blocks internal assets. Adding ‘unsafe-inline’ does work but defeats the object of setting the headers.
I’ve set my CSP to report only while I compile the policies. Here’s what i have below for allowing Google if you need them. I’m setting mine via php rather than htaccess.
header("Content-Security-Policy-Report-Only: default-src 'self' https:; script-src 'self' 'unsafe-inline' ajax.googleapis.com www.google-analytics.com www.google.com www.gstatic.com maps.googleapis.com; style-src 'self' 'unsafe-inline' fonts.googleapis.com; font-src data: fonts.gstatic.com 'self'; img-src data: www.google-analytics.com 'self' secure.gravatar.com"); // FF 23+ Chrome 25+ Safari 7+ Opera 19+ header("X-Content-Security-Policy-Report-Only: default-src 'self' https:; script-src 'self' 'unsafe-inline' ajax.googleapis.com www.google-analytics.com www.google.com www.gstatic.com maps.googleapis.com; style-src 'self' 'unsafe-inline' fonts.googleapis.com; font-src data: fonts.gstatic.com 'self'; img-src data: www.google-analytics.com 'self' secure.gravatar.com"); // IE 10+Hopefully the ‘self’ issue will get resolved.
Thanks
TJ
December 18, 2019 at 12:27 pm #1167247by the way ‘self’ is ok but unsafe-inline and unsafe-eval are not ok – but on most of wordpress installation they are needed to have a working Site
March 13, 2020 at 9:32 am #1192845Guten morgen,
gibt es eine vernüftige htaccess file Einstellung wo Enfold auch mit allen Funktionen noch funktioniert ? Gerade der Bereich Header “set Content-Security-Policy” ist ja diesbezüglich individuell konfigurierbar. Ich finde es sollte die Aufgabe des Theme Entwicklers sein dies gewährleisten zu können.
March 13, 2020 at 1:03 pm #1192868Eben weil es zuviele Webseiten Einstellungen jeder einzelnen Seite gibt, kann das Thema das nicht komplett leisten.
Siehe hier mein Kommentar: https://kriesi.at/support/topic/header-security-entries/#post-1153969
Mein Einwand war, auf einem Frischinstalliertem Enfold ohne Google Services etc. Ohne Plugins – wohl aber mit Inline ( child-theme functions.php) Scripten die Header set Content-Security-Policy Diese Scripte obwohl ja auch auf meinem https laufend blockiert.
???
_____________Precisely because there are too many web page settings of each page, the theme can’t do it entirely.
See here my comment: https://kriesi.at/support/topic/header-security-entries/#post-1153969
My objection was, that on a freshly installed Enfold without Google Services etc. Without plugins – but with Inline ( child-theme functions.php) scripts the Header set Content-Security-Policy blocks these inline scripts without the allowance to be unsafe-
This reply was modified 5 years, 4 months ago by
Guenni007.
March 13, 2020 at 1:15 pm #1192873Hallo Guenni007,
Ja Guenni007 das mag wohl sein – das jedes Enfold individuell eingerichtet ist. Aber mit den Standarteinstellungen ohne GA, GM etc. Also nur Enfold mit Layerslider etc, wäre es wichtig. Weil wir haben jetzt Ärgern mit einem Kunden, dem wir eine Webseite gemacht haben und dieser moniert jetzt die Seite wäre nicht sicher. Der Mitarbeiter ist zwar total inkompetent – was das angeht und ein Wichtigtuer hat einfach bei die Webseite mal mit https://siwecos.de/ testen lassen – und ist jetzt der Meinung wir wären da in der Pflicht – sämtliche Geschichten zu beheben. Bei https://siwecos.de/ erreicht die Webseite auch 82 vom 100 Punkten, aber was ich nicht so ohne weiteres Lösen kann ist die CSP Geschichte. Zudem bei der applikation siwecos – auch angezeigt wird das der “DOMXSS Scanner” dort “Unsicheren JavaScript-Code verwendet wird” anzeigt. Aber es ist ein Standart Enfold mit WP. Aber erkläre das mal einem Mitarbeiter oder den Chefs!.
translated with google translate
Hello Guenni007,Yes Guenni007 that may well be – that each Enfold is individually decorated. But with the standard settings without GA, GM etc. So only Enfold with layer slider etc, it would be important. Because we are now having trouble with a customer who we have made a website for and who is now complaining about the page would not be safe. The employee is totally incompetent – as far as that is concerned and a junk has simply had the website tested with https://siwecos.de/ – and is now of the opinion that it would be our duty to fix all the stories. At https://siwecos.de/ the website also achieves 82 out of 100 points, but what I cannot easily solve is the CSP story. In addition, with the siwecos application – the “DOMXSS Scanner” is also displayed, indicating that “Unsafe JavaScript code is used”. But it is a standard Enfold with WP.
-
This reply was modified 5 years, 4 months ago by
justbusy.
January 15, 2021 at 3:34 pm #1272755Hello,
i have achieved this by adding this at the end of the functions.php. In case your htaccess gets ignorted by the hoster:
header('Strict-Transport-Security:max-age=15768000'); header('X-Frame-Options: SAMEORIGIN'); header('X-Content-Type-Options: nosniff'); header('X-XSS-Protection: 1; mode=block'); header("Content-Security-Policy: default-src 'self' 'unsafe-inline' 'unsafe-eval' https: data: *.YOURDOMAIN.com");-
This reply was modified 4 years, 6 months ago by
kopf-und-stift.
January 18, 2021 at 5:02 pm #1273373Hi kopf-und-stift,
Glad you got it working for you and thank you for sharing! :)
If you need further assistance please let us know.
Best regards,
Victoria -
This reply was modified 5 years, 4 months ago by
-
AuthorPosts
- You must be logged in to reply to this topic.